The Dude's Guide to Certificates in Sitecore Experience Commerce 9
If you've had a chance to install Sitecore Experience Commerce 9, you would have realised that a range of certificates are generated during the install process. And you may be wondering- what the $@#! are they all used for?
Fear not. I'll talk you through each of them. In a nutshell, there are three different types of certificates that are required. Each of them serves a unique purpose.
Certificate for IIS Sites
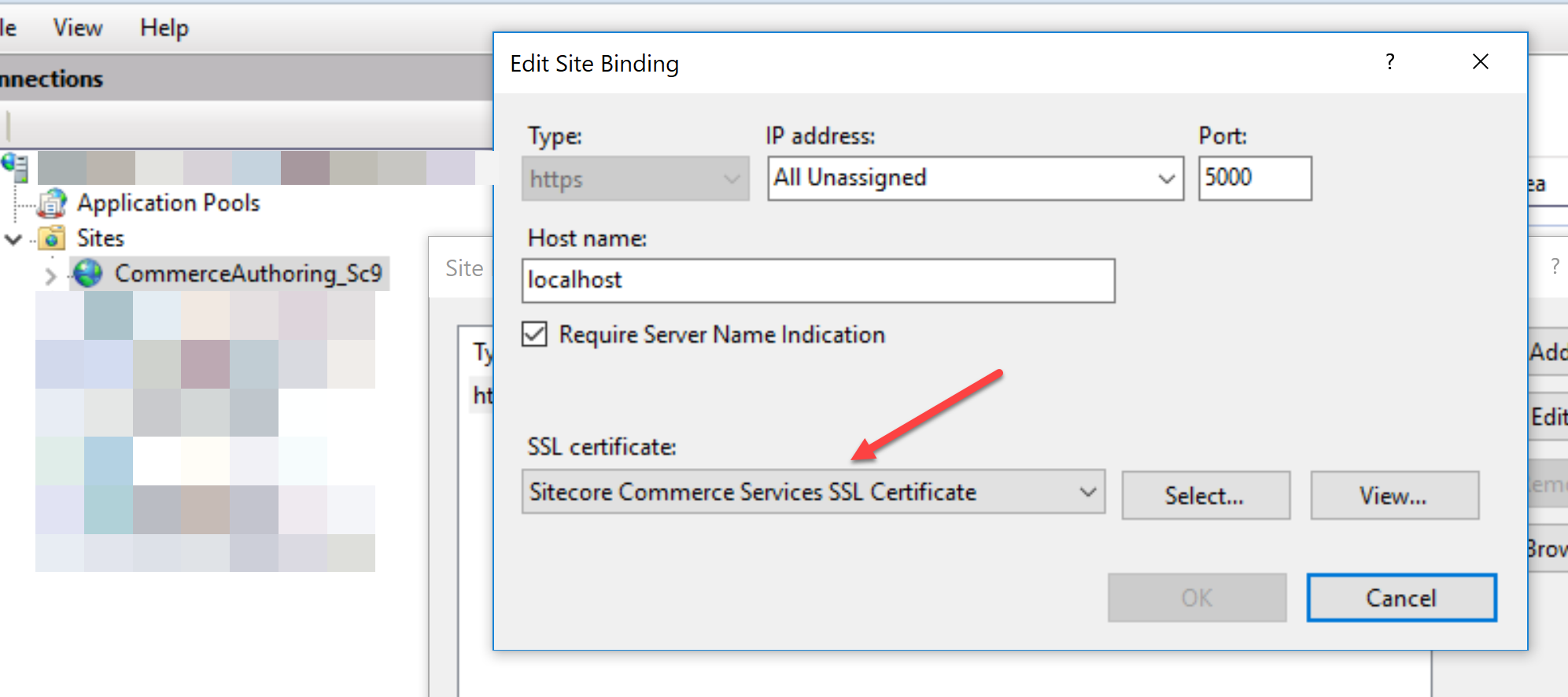
The certificate associated to the Commerce Engine IIS websites is an SSL server certificate. This is required to encrypt all traffic to/from the Commerce Engine, Sitecore BizFx (Business Tools), and Sitecore Identity Server over https. For development purposes, a self-signed certificate with CN localhost is created. Once you change the hostnames for production use, you can get your own SSL certificate and update the binding.
Identity Server Certificate
This is a code signing certificate and is used by Sitecore Identity Server to sign and validate identity and JWT access tokens. Business Tools users are authenticated against the Identity Server and this is where it comes into play.

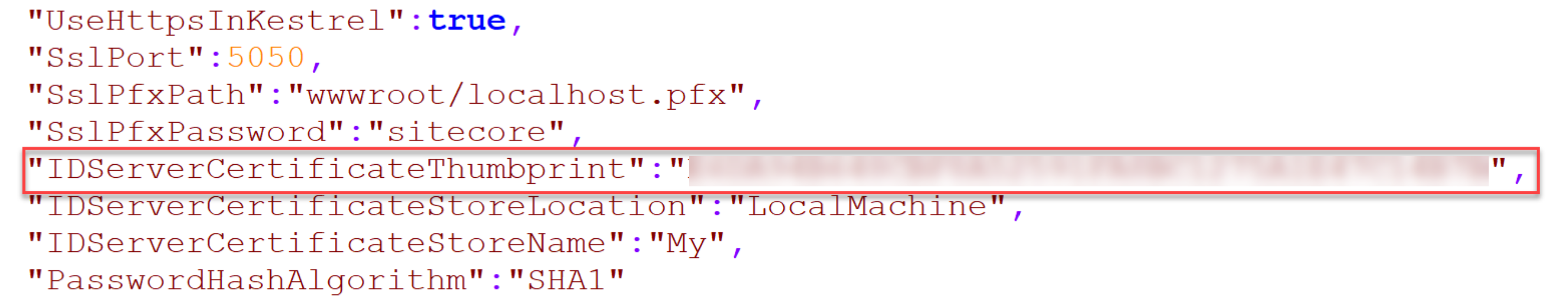
The thumbprint for this certificate is configured in your Identity Server wwwroot\appsettings.json file.
Sitecore Commerce Engine Connect Certificate
This is an SSL client certificate required to authenticate clients to Commerce Engine using certificate authentication. Commerce Engine Connect uses this to get access to the Commerce Engine. Calls made to Commerce Engine, eg. by the SXA Storefront go through Commerce Engine Connect. An X-ARR-ClientCert header is added to requests with the certificate information such as thumbprint to authenticate the call.
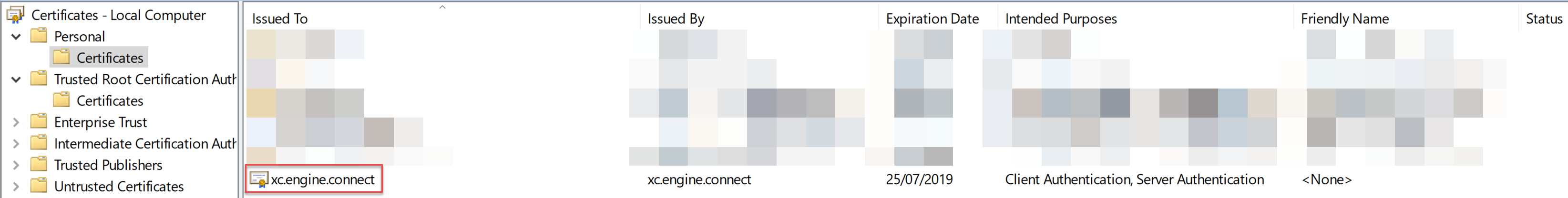
Once you install the certificate to your LocalMachine Personal Certificate store, you also need to add it to IIS Server Certificates. The thumbprint of this certificate is configured in Commerce Engine in wwwroot/config.json.
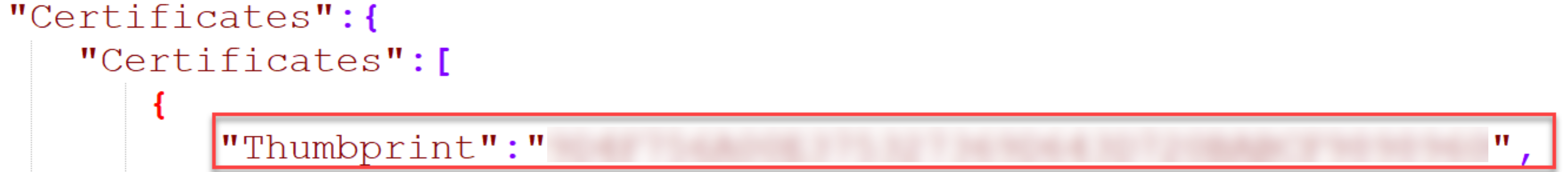
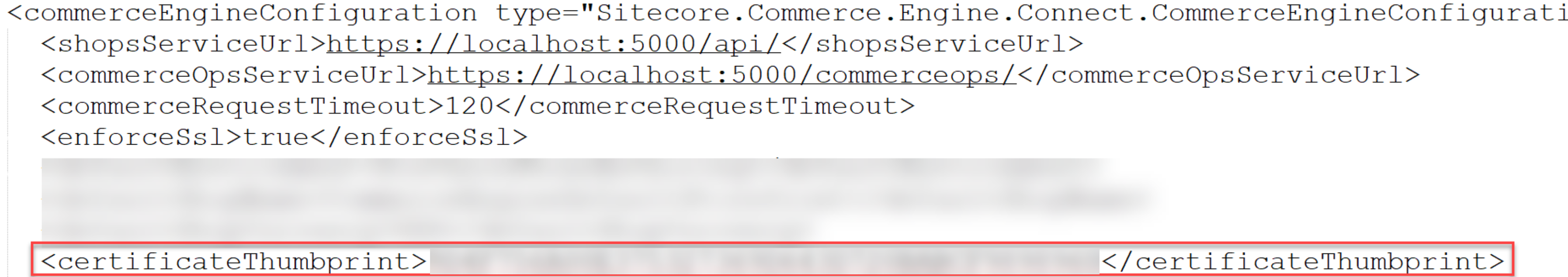
And the same thumbprint is configured in Commerce.Engine.Connect.config for Commerce Engine Connect (the client).